Setting up a guest network with the EdgeRouter Lite
I recently purchased a Ubiquiti Networks EdgeRouter Lite to act as the router to my home network. As this box is only a router and not a WiFi access point, I'm using my Apple Time Capsule as an access point. By doing this and not using the Time Capsule, I lost the ability to have a separate guest network that wouldn't interact with my main network and wouldn't have access to my internal resources. After a bit of searching, I found out that the Time Capsule (and Airport Extreme)'s guest network uses a VLAN tag of 1003. A VLAN is a virtual LAN designed to separate traffic without physically separating it. I knew that the EdgeRouter Lite was extremely powerful and could do all kinds of wacky things with a VLAN; the question was just how could I do it.
I've been dabbling with Linux networking for almost 20 years, so firewall, DNS, DHCP, etc. don't scare me. It was just a matter of putting the right pieces in the right places without having to resort to the command line.
Here's what I did:
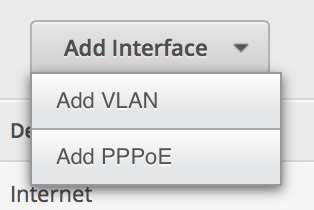
- From the Dashboard, click Add Interface and select VLAN.
-
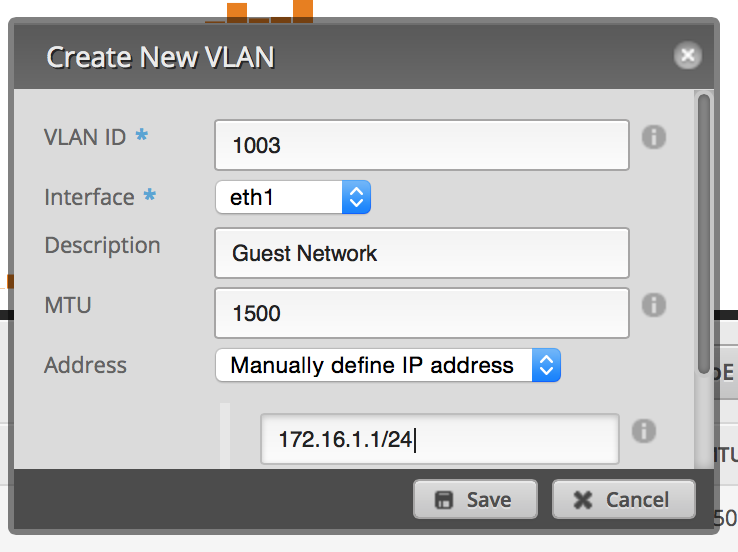
Set up the VLAN as 1003 and attach it to the physical interface of your LAN. Give it an IP address in the range of a private IP block, but make sure you end it in a /24 to specify the proper subnet (I originally did /32 as I though it was supposed to be the exact IP address).
-
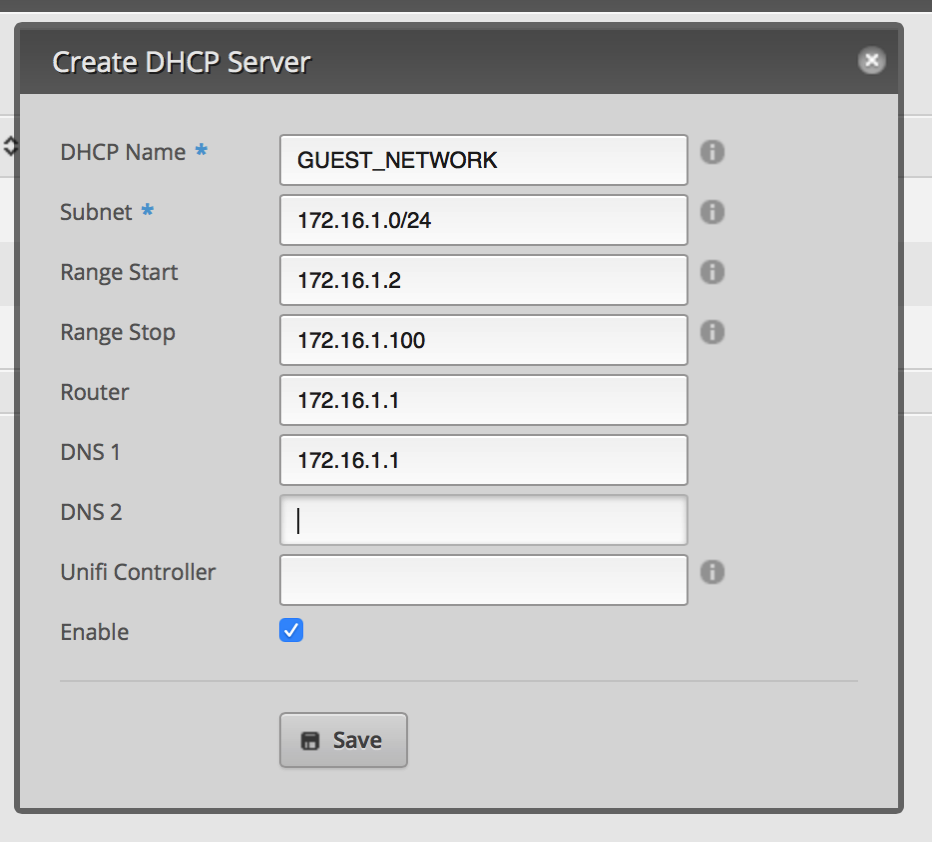
Click on the Services tab. Click Add DHCP Server. Set it up similar to the image below.
-
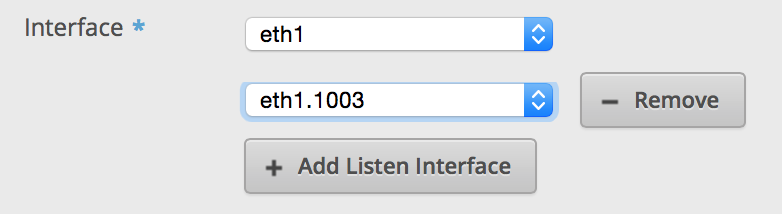
Click on the DNS tab under services. Click Add Listen interface and select the VLAN interface. Make sure you hit save.
At this point, you should be able to connect to your Guest Network and connect to the Internet. However, you'll be able to access the EdgeRouter as well as other devices on your LAN. Next thing you have to do is secure the VLAN.
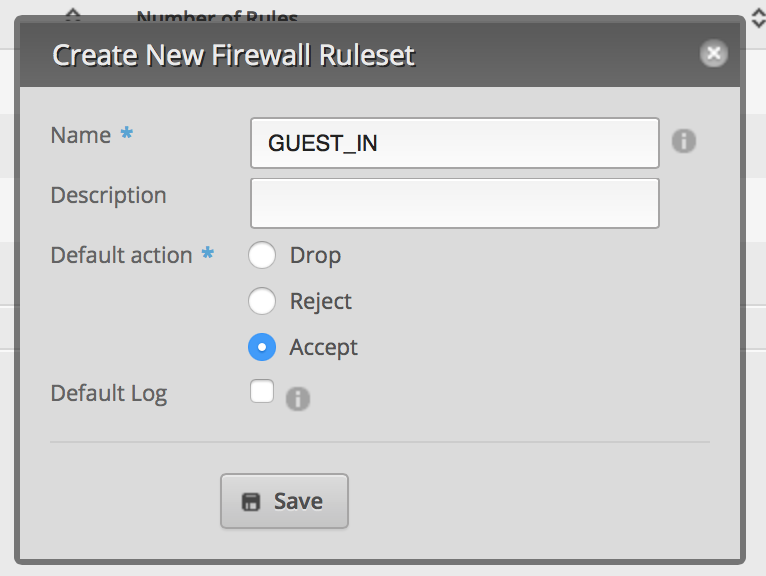
- Click on Firewall/NAT and then click on Add Ruleset. This is for packets coming into the router destined for somewhere else (not the router). Set up the default policy for Accept. Click Save.
-
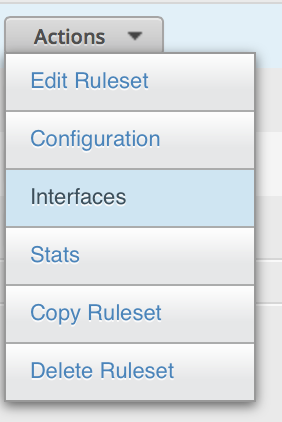
From the Actions menu next to the Ruleset, click Interfaces.
-
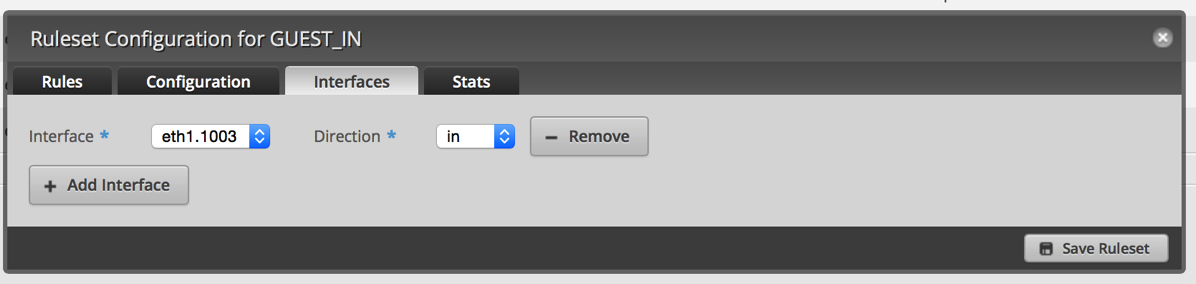
Select your VLAN interface and the in direction.
-
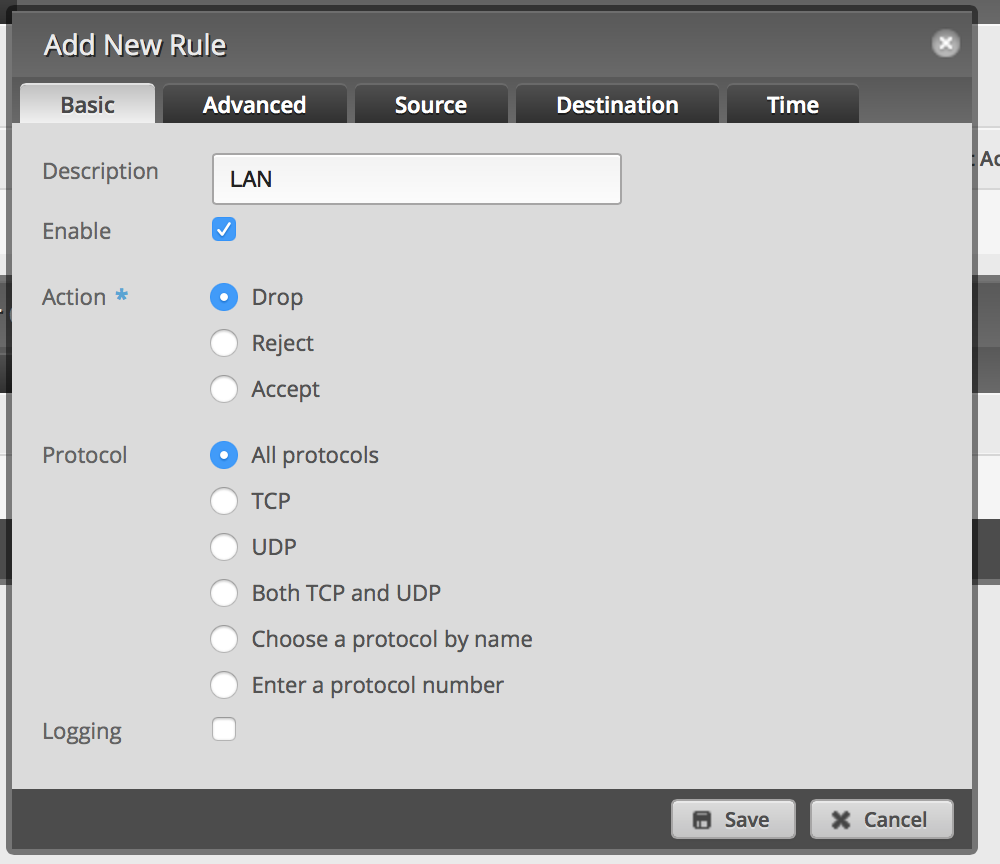
Click Rules and then Add New Rule. Click on Basic and name it LAN. Select Drop as the Action.
-
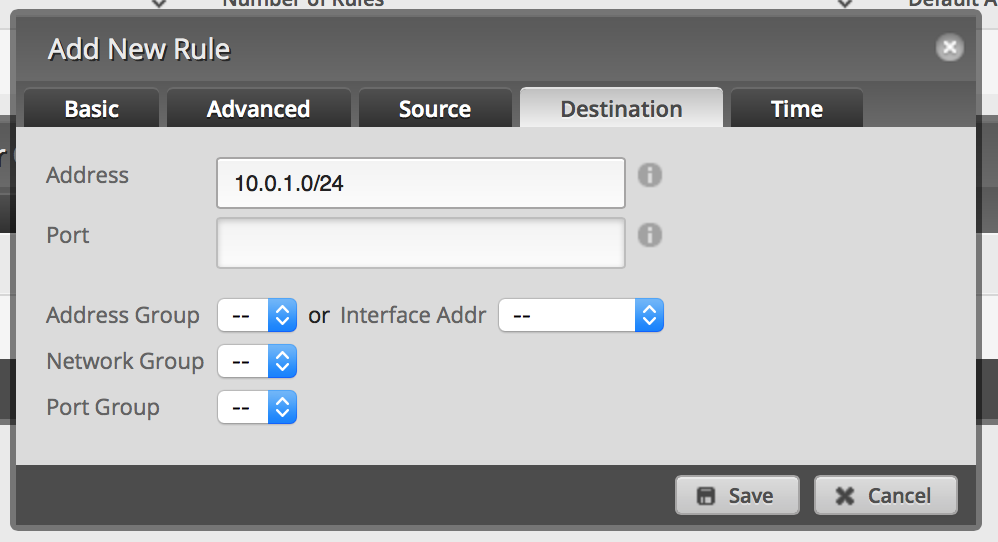
Click Destination and enter 10.0.1.0/24 or whatever your LAN IP range is. Then click Save. This will drop all packets from the VLAN destined for your LAN. Save.
-
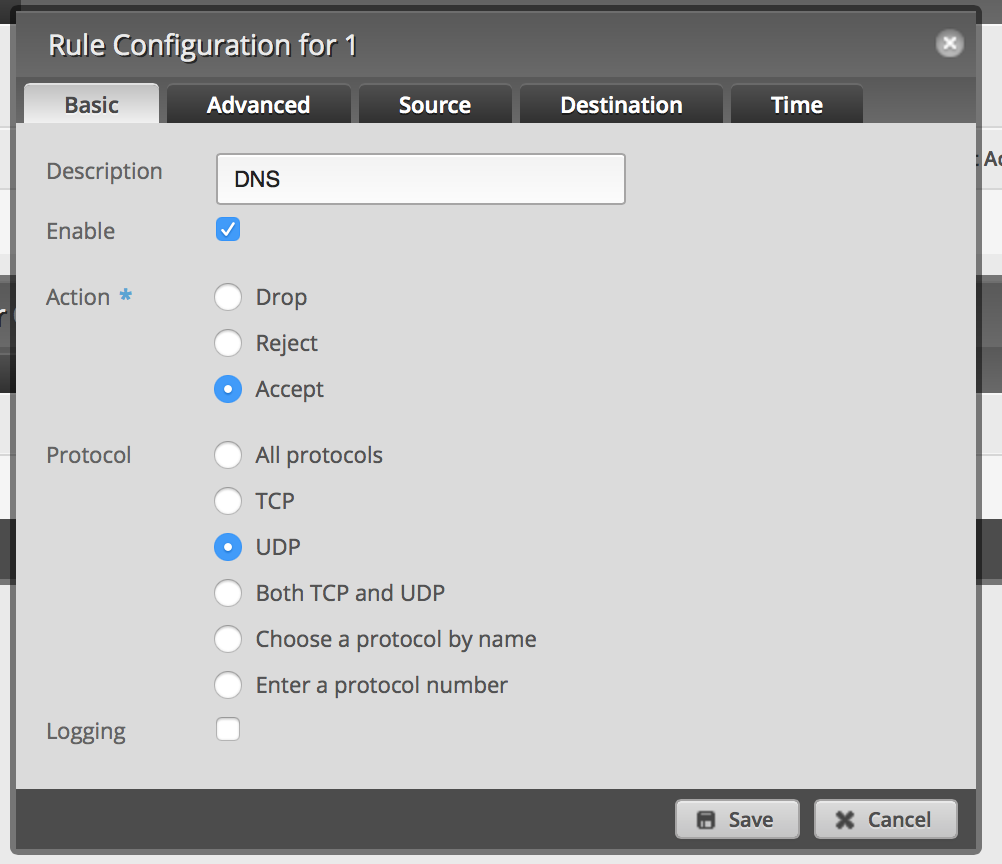
Repeat 1 and 2 above (name it GUEST_LOCAL). From the Interface, select the VLAN interface and the local direction. However, set up the default policy as Drop.
-
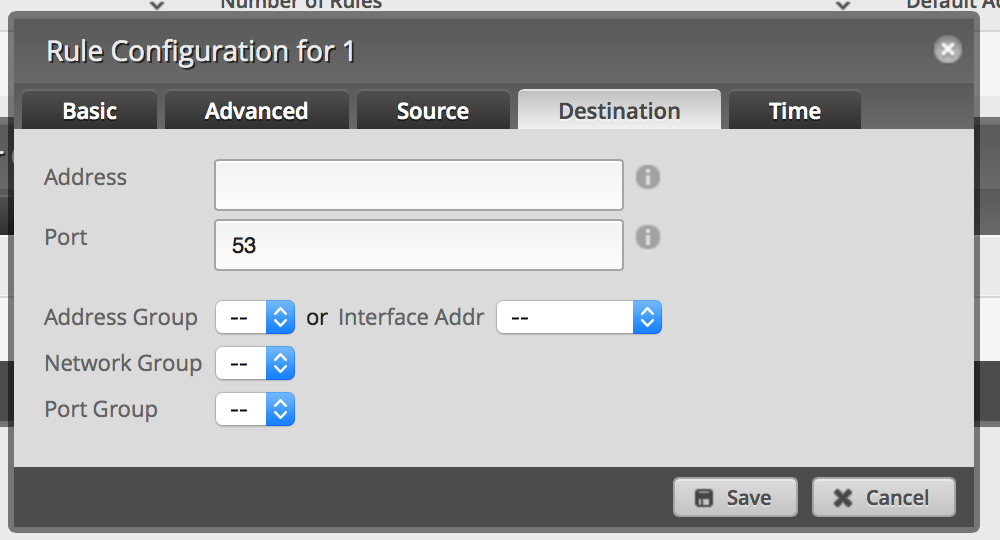
Add a new rule. Set it to Accept on UDP port 53.
-
Save.
Now you can test this by connecting to the guest network and accessing the Internet. Then try connecting to a device on your LAN or connecting to the EdgeRouter Lite. Both actions should fail.
I've tested this and it is working well on my network; if I've missed anything, please let me know!
Comments
Did you find a way to limit the bandwidth on only the guest portion of your network?
I haven’t tried, but I suspect Smart Queue Management could let you do this.
Thanks for this guide! I just got an Edgerouter X (so I’m new to the EdgeOS platform) and it worked perfectly.
Have you seen this?
I also have an airport extreme + edgerouter lite.
Using my iphone/macbook when I join the guest network (192.168.200.0/24) I get an ip address from my privileged network (10.0.1.0/24). It seems as though osx tries to get a new IP via DHCP but fails and reverts to its old one. Not sure what to do to force it to get an IP on the correct subnet.
My windows machine doesn’t seem to have this problem.
I haven’t seen that except when my Mac is plugged into Ethernet and joining WiFi on my guest network. You can have your device forget the privileged network and then join the guest network to see what happens. All of my iOS devices and Macs work properly on either network.
Thanks Scott, it was great to find you old post on this topic… I have a new v1.7 ERL and am attempting to isolate a VLAN for guests (eth0-WAN, eth1-192.168.1.1/24; eth2 -192.168.2.1/24; eth2.30 - 192.168.3.1/24)
My GUI interface is a bit different than you described above… but close enough… Question: I am a bit confused as to the IP (destination) specification. (I can’t attache a screen shot to show my case…) I have Rules # 1 and 2; 1: Description “UniFI Portal, Destination: address 192.168.1.100, port-group, UniFi_Guest Portal, Protocol tcp, action accept. 2: Description “Drop Route to Private Network 192.168.1.0, Destination 192.168.1.0/24, Protocol all, action drop.
I have loaded this from an example I found in a forum… but am unsure if it is established correctly for my case.
Can you verify/recommend changes?
I appreciate your time/insight.
Jeff
Should my rule destination be the VLAN I want to isolate?? (eth2.30)??
In step 5, the destination is your LAN, not your Guest Network. You’re basically saying that you want all traffic that comes from the guest network (Step 3) to be dropped when it hits the LAN (destination). I believe you’ll have to make sure that the Guest Portal rule is before the drop rule otherwise traffic will get dropped and won’t reach the portal.
Great Article! I was just about to give up & I found your blog. I have the exact same setup & followed your instructions exactly. That being said, it looks like it almost works for me. Unfortunately, from an android phone I get an IP, but mobile chrome states the the webpage is not available, with a sub note stating: DNS_PROBE_FINISHED_BAD_CONFIG (DNS Lookup Failed). I need to test a few other devices, but it seems to be repeatable as the behavior is the same on an iPhone as well. This tells me I did something wrong with the last few steps or have a different setup for DNS. Help!
EdgeRouter lite (OS v1.8) + Airport Extreme (AC v7.7.3)
Thoughts?
Hi Aaron,
While I haven’t upgraded to EdgeOS 1.8, I suspect that the problem is the firewall rule for DNS. Look at Steps 6 & 7. You need have a rule that comes from the VLAN to the router (local); without that rule, you’re blocking DNS requests.
Hope that helps.
Thanks for the quick reply! Followed steps 6 & 7 to how I understand them. Summarized below.
| GUEST_IN: eth1.1003/in | number of rules: 1 (LAN Drop All) | from 192.168.1.0/24 |
| GUEST_LOCAL: eth1.1003/in | number of rules: 1 (Accept DNS Port 53 - UDP) | w/ no address listed & blanks for all drop downs |
Sound right? Feels like I am missing something.
CLI Clip: firewall { all-ping enable broadcast-ping disable ipv6-receive-redirects disable ipv6-src-route disable ip-src-route disable log-martians enable name GUEST_IN { default-action accept description “” rule 1 { action drop description LAN destination { address 192.168.1.0/24 } log disable protocol all } } name GUEST_LOCAL { default-action accept description “” rule 1 { action accept description DNS destination { port 53 } log disable protocol udp } } name WAN_IN { default-action drop description “WAN to internal” rule 10 { action accept description “Allow established/related” state { established enable related enable } } rule 20 { action drop description “Drop invalid state” state { invalid enable } } } name WAN_LOCAL { default-action drop description “WAN to router” rule 10 { action accept description “Allow established/related” state { established enable related enable } } rule 20 { action drop description “Drop invalid state” state { invalid enable } } } receive-redirects disable send-redirects enable source-validation disable syn-cookies enable }
Aaron
So I think I got it working… I had to enable DNS forwarding for the eth1.1003 vlan interface
dns { forwarding { cache-size 150 listen-on eth1 listen-on eth2 listen-on eth1.1003
Make sense? Need to test now. ;-)
Ah, yes. I have this as well and must have missed it on my right up. Thanks for the correction!
Hi Scott, Thanks for your post. It is a really slick way of handling the configuration where a user has one internal network and needs to make it inaccessible.
In my house I have multiple networks (Home LAN, management LAN, VoIP LAN, etc). I understand that I should be able to accomplish what you showed by following steps #4, and #5, for each of the internal networks.
I’m quite a newb when it comes to FW rules, but I was wondering if instead of saying:
- allow everything, and then saying, drop it for this and this and this;
there is a statement that says:
- drop everything except for traffic going out towards eth1 (my ISP interface)?
Thanks,
Stevan
As others have pointed out to me, is there a need to have multiple VLANs besides guest and main? With my current equipment I can have separate VLANs for different WiFi SSIDs and even ports on my switches, but what does it accomplish in a home setup? Your configuration, of course, is different. For me, I still haven’t figured out why to have different VLANs on my home network.
Yes, for FW rules, you can specify a default rule and in my case for the guest network to my router, I say DROP everything and then allow DNS.
Good luck with your configuration!
my wan is on eth0 my lan is 192.168.1.0/24. eth1 i have lan2 as 192.168.2.0/24. eth2 now lan2 feeds another router that unfortunately defaults also to 192.168.1.0/24. is there a way to separate the lans so lan and the other router both can give out addresses in the 192.168.1.0/24 range and never interact with each other?
Do you need a separate router? You should only have 1 DHCP server per physical LAN segment. If you have the other router’s WAN port hooked to the 192.168.2.0/24 network, you’ll have a double NAT which you probably don’t want.
You might ask on the Ubiquiti forums for help as I’m a bit lost in your setup.
i use a pfsense firewall just for a vpn attached to lan2. i’ve never had a double nat issue. normally i change the ip address of pfsense to say 192.168.3.0/24, but i was just wondering if it could be done. is the procedure you wrote about the same that i would use for eth1 and eth2 since i don’t have vlans?
thanks for the help.
I suspect it would be, but don’t have experience with your kind of setup.
just one last question . . . forget the second router part. i have eth1 as 192.168.1.0/24 and eth2 as 192.168.2.0/24. i can access eth1 from eth2 and vice versa. there must be a firewall rule so that they stay separate. like your guest can’t access eth1.
Sure, looked for the references to the VLAN (eth1.1003) and change them to eth2.
Scott, thanks for your very helpful post. I’m deploying this kind of setup shortly. Are you using the Airport/TC is router mode? If so, you give up some mgt/visibility of Airport clients from ERL, no? My understanding is that Airport can only offer its guest VLAN if it’s operating as a router vs bridge.
Hi Jonathon,
While I’m no longer using a Time Capsule for wireless (I’m using UniFi equipment), I did have the Time Capsule in bridge mode and had a guest network on it. The Time Capsule guest network creates a separate VLAN (1003), but without a router to handle a VLAN, the guest network does nothing. If you just turn on the Guest Network on the Time Capsule without setting up the VLAN on a separate router (when in bridge mode), traffic won’t go anywhere.
I’m going to try the TC/AP solution next week. My long-term plan is, like you, to try a UniFi AP, but only after I buy a PoE switch. Thinking I should have gotten the ER-PoE switch… but I’m getting ahead of myself. Any recommendations on the UniFi AP model? Perhaps a blog post is coming.
Hi Jonathan,
As I never have enough ports, the ER-PoE wouldn’t work for me! I wrote a review of the UniFi AP models. That doesn’t include the Pro model which I have yet to review. I am using a Pro and an LR. I have another Pro on the shelf that I haven’t installed and haven’t decided if I want to replace the LR with the Pro. I don’t think you can go wrong to the UniFi APs.
Thank you so much for this post! I realize I should probably get around to learning the CLI but I really wanted to be able to do this via the GUI and the 1.8 firmware made it seem like it should be possible. After nearly giving up when every resource I found directed me straight into the CLI or to pre-created config files, I found your post, followed the instructions, and everything worked perfectly.
Scott, thanks so much for all your blog posts! I got my ERL and Airport running with private VLAN. Now, I think I need to pick up a managed switch. Don’t yet need PoE, but would like to future-proof my purchase. Do you still recommend the Cisco SG300-10P? I see the Cisco SG300-10PP at B&H Photo for under $200. Any other managed recommendations? Thanks!
Hi Jonathan,
I recommend the UniFi Switch; the 8 port model (with 2 SFP ports) is $199 and can be managed with the UniFi controller software. While the Cisco switch can do magical things, it is far too complicated for me. Once I find the UniFi Switch 16 in stock, I’m going to get one of those. My review of the 8 port model is here.
For the most part, managed switches are overkill for a home setup. However, I just turned on a VLAN on one of my ports yesterday to isolate some of the broadcast traffic.
Hi Scott, I am in a process of upgrading my network equipments removing all off the shelves AP to Unifi AC Pro, LR , Cloud key and some Unifi in Wall Plus Edgerouter Lite(still thinking) and unifi switch 8(buying this because Cloud Key doesn’t work on edgemax and for Unifi AP). My current router pfsense running on old IBM PC with P4 CPU. Is it worth to upgrade from pfsense to Edgerouter lite? You said you had Almond + which I also have been using it as AP but you said you didn’t use it as router and instead you went with edgerouter Lite while the spec of Almond + shows that it is using the same CPU and higher frequency than edgerouter Lite so why Edgerouter lite is better ? Last what is the best 8 ports unmanaged switch that I will not regret to purchase ? Thanks
Would appreciate any suggestions
Hi Marthad,
I’m in the process of moving all my networking equipment to UniFi. This weekend I replaced an unmanaged switch and a Cisco PoE switch with a UniFi Switch 16. I also have 2 UniFi AC Pros and an AC LR. My router is still an EdgeRouter Lite, but I have a USG on the shelf that I’m going to put into the network after there are a few more updates to the UniFi controller (I want a GUI for static DHCP entries, IPv6 support, and the ability to use the 2nd port for a second LAN). The management of the UniFi line is why I really like it; even though there isn’t much management required, I like being able to see statistics and having complete control.
I’m not familiar with pfsense, but I like the dedicated hardware of the UniFi line (and currently the EdgeRouter Lite). The Almond+ is an interesting product, but still doesn’t seem like it is ready for prime time last time I looked at it. The way the UniFi network seamlessly works together makes it attractive even if this is just my home network. My house isn’t all that big, but with the UniFi gear I have, I get excellent WiFi coverage everything and it is rock solid.
My EdgeRouter Lite has been running for over 5 months without a reboot; even though I plan on moving to the USG in the future, I still recommend the EdgeRouter Lite if someone isn’t buying into the UniFi line. If you want to tweak the router, the USG may not be the best choice as the GUI interface is limited and command line configuration is trickier than the EdgeRouter Lite.
For me, unmanaged switches are a dime a dozen. I’ve had a Linksys, Netgear, and TrendNet that all performed fine. I’ve retired all the unmanaged switches not because they failed, but because I like statistics and with the managed switches, I can get per port statistics and can setup VLANs if needed (I have 1 VLAN for my VeraEdge that seems to have made it much more stable).
Feel free to ask more questions.
In step 6 where GUEST_LOCAL is created by repeating step 1 and 2, should it not be drop? If accept is used as in step 1 and 2 the guest network can access the router.
I’ve updated the post with your correction. The default is Drop (I think) and I overlooked that I said to change the default policy to Accept in step 1. Thanks!
Thank you for a great guide, helped me set up my router and understand how it works.
You’re very welcome!
Assuming the GUEST_LOCAL for step 6/7 is to ensure DNS Port 53 ? This affecting anything if I just use my ISP’s DNS (sorry it’s late I’m sleep deprived and setting up an EdgeRouterX with a few Ubiquiti AP’s where we want an isolated public WiFi) - assuming that without Step 6/7 even Port 53 is blocked when using an outside DNS service??
Yes, if you are passing your ISP’s DNS to the guests, then you don’t need to open up port 53 into the ERL.
Thanks a lot for this, but I just can’t seem to get it working. When I apply the above, I just don’t have internet on the guest network. I have PPPoE0 internet for which I do the source NAT translation masqueraded to my private source IP range. When I also apply this same rule to the guest network IP range, the guest network does have internet connection but can also see my private IP range even though I created the exact same firewall/NAT rules as stated above. What am I doing wrong? I’m kind of a newby at this. Help is much appreciated.
Hi Mark,
Unfortunately I’m not familiar with PPPoE or your setup with your NAT translation. My setup with my ISP is pretty basic and the stock configuration for NAT works fine for me. Maybe someone on the Ubiquiti forums can assist you.
Okay, I will continue my search. Thanks for your reply anyway!
Hi, I did VLAN on eth4, and it does not work. The client who get directly connected gets IP but does not ping (firewall allows all traffic). I think, can it be related to VLAN tagging (where packets are modified)? if so, can I chose tag or not tag vlan on eth4?
YOU MISSED THE ALLOW DHCP (PORTS 67-68)
I have a Netgear managed switch between my Airport Extreme and my EdgeRouter Lite. I tag the port that the AE is plugged into, but I never get an IP address for the ER. If I plug the AE directly into the ER, it works fine (but the rest of my house becomes useless).
Anyone have any ideas?
Hey Bob,
I believe you need to setup DHCP relay. See https://help.ubnt.com/hc/en-us/articles/204962294-EdgeMAX-Set-up-DHCP-relay-on-interfaces or http://www.brocade.com/content/html/en/configuration-guide/nos-601-l3guide/GUID-582F3B3C-4E4A-492D-A5B6-161ADC27D789.html or https://www.brocade.com/content/html/en/configuration-guide/nos-601-l3guide/GUID-582F3B3C-4E4A-492D-A5B6-161ADC27D789.html
Overview @ https://www.youtube.com/watch?v=jPfZJNRJYM0 Also see http://www.tech-faq.com/dhcp-relay-agents.html
Great articles I find on your blog, Scott. Thanks for that. Will try to visit your site regularly. Do you have any experience with policy based routing on ERPro? Talking about tailor-made balancing of the load on two WAN interfaces. Would you suggest a well written readout or perhaps point me to your own content? Would be appreciated most probably not only by me. :-)
Merry Christmas and Happy New Year for you with family and all your readers, cheers.
I haven’t done policy based routing as I only have 1 WAN connection. This article is a bit outdated as I no longer use the Time Capsule and setting up the guest network with all Ubiquiti gear is so much simpler.
Hi Scott,
I just wanted to say thank-you for this write up. I have an ER-Lite and Cambium e400 wireless access point and your instructions were really clear and easy to follow. Once I had the set-up on the ER-Lite i just needed to create a new SSID on the Cambium with the corresponding VLAN ID and I now have a guest Wi-Fi network without access to my LAN.
Cheers Simon
Scott, Great. Post, I’ve read over the comments and I see now you have a LR-AP. I’m trying to setup the EdgeRouter with the LR-AP to have a separate guest and private wlans. Do you a similar configuration and would you share your insight (or config) in getting it setup?
Hi Matt,
I actually do have a post at http://blog.gruby.com/2016/07/13/guest-network-with-edgerouter-lite-and-unifi-access-points-take-3/.
Note however, you don’t need to have a separate guest VLAN. The UniFi’s guest network does client isolation which means guests can’t access your private network. However, I still use a separate VLAN for my guest network as I’ve described in the post.
Good luck!
This works but you an still ping the ip address of the router on the main network and get a reply.
Hello Scott! Been using your configuration for a while and it has been working great inside my small office. I created my main lan for the admin area and one vlan 10 to give internet access to guests. Now the thing is that i’ve finally managed to have a secondary internet access and I was about to configure the edge router lite for load balancing. So, I launched the wizard, I selected Load Balancing, and I set eth1 and eth2 as internet port and eth0 as lan port (192.168.1.1). Now, everything works perfectly with the internal LAN, the computer from the administration get the right IP address, internet connection works fine, speed and stability increased too…but the problems come with the Vlan! I followed again step by step your configuration, by creating a Vlan 10 on interface eth0 and a Guest DHCP as described in the video. Apparently everything seems to work fine for the guest access, meaning that the devices connect to Unifi access points (with SSIDs confgured with VLAN) get the correct IP (192.168.3.x) but they don’t get any internet access ! The weird thing is that as soon as I disable one of the two wan interface (eth1 or eth2) the computer on the guest Vlan immediately get access to internet. So…can you help me with that? Is it needed an extra rule or configuration in order to have 2 working WAN (load balance) and 1 vlan for guest access? Many thanks in advance!
Hi Stefano,
Unfortunately I’ve never used a dual WAN configuration. I’d post a note in the Ubiquiti forums or contact their support as your use sounds pretty common.
Thanks for your time Scott. I wanted to create a topic on Ubiquiti forums but the problem is that those guys usually run configuration via CLI and I’m not familiar with it :D Anyway, I’ll see searching on the web and I hope I’ll find a solution :D
Thanks again!
The CLI is your friend! It may take a little while to get used to the EdgeOS syntax, but it is pretty use to use.
Stefano,
I had exactly the same issue with Dual WAN configuration. Take a look at this post https://community.ubnt.com/t5/EdgeMAX/WAN-Load-Balancing-HTTPS-Failover-amp-Inter-VLANs-traffic-amp/td-p/1120684
Basically, you need to add “modify balance” FW rule under each vif. The rule itself is already there if you run dual WAN wizard, you just need to assign it to your vlans. I’m not sure if that could be done through GUI, it’s easier to download your config file and edit it in a text editor, then upload it back to the router.
Interesting page. I am just looking into the EdgeRouter Lite to separate the ‘router’ function from my Apple Time Capsule ac. The limitations of the Apple router seem addressed by the UBNT EdgeRouter Lite.
more processing power no reboots to fix advanced options VPN server setup support ssh access – don’t know about remote ssh ability with the EdgeRouterLite DPI (Deep Packet Inspection)
I guess my plan is to remote the router from the TimeCapsule. Leave it as a AP and use the switch and another unmanaged switch (Netgear 8 port GigE). Leave it for Time Machine backups as well .. for now.
Maybe DIY RaspberryPi Time Machine might be a fun project
Eventually I guess replace more gear with a Mesh Wifi from UBNT.
Did you ever try to use the Guest Network and wifi network of the Time Capsule with the EdgeRouter lite?
Yes, see this post. I no longer use the EdgeRouter Lite or Time Capsule, but the article should still be fairly accurate.
Hi there, great article and really helped me.
Having looked at the approach here would it also be possible to have a default block policy and only then allow access to networks? That way nothing gets through by accident and only through a positive exception.
Scott, you’re not using ERL anymore? What replaced it? Thx!
I’m using the USG (UniFi Security Gateway) which is basically identical to the ERL in terms of hardware, but managed using the UniFi Controller which is used to managed my switches and access points.
Doh. I forgot you wrote that up…
Dan…than you so much, you saved my life! I’ve only read your post yesterday, I followed the steps in your link and finally the load balancing is working on VLANs too.
PS. Thanks for telling me also the easiest way to edit the config file, it took few minutes and it was done!
Scott,
This is a TREMENDOUSLY HUGE post. Thank you for making the edgerouter great again.
Ok seriously though, this was a great post. I have the same set up as in the tutorial, so getting the vlan up and running was easy. I actually am planning on using the VLAN for my smart home devices such as Alexa or my Wifi electronic plugs. For example, I have a TPLink HS105 that works with Alexa, however, it requires cloud access enabled for Alexa to work. Why this is the case, I have no idea, however, it almost feels like I’m purposing introducing a huge security risk into my network. If hypothetically a hacker was able to connect to the Wifi plug from the outside and execute some sort of code, I believe this Guest VLAN set up would add an additional layer of security preventing the wifi plug (or Alexa) from directly pinging or detecting the other devices on the LAN. Plz let me know if you agree.
Interestingly enough, when I connect to the VLAN on my laptop, i cannot ping any devices (as expected), however, Alexa works and is able to turn on/off my wifi plugs without issue.
Thanks again!
Best, RP
Hi RP,
I’m glad that my post was helpful. VLANs are tricky. I have moved most of my IoT gear to a separate VLAN and setup firewall rules to restrict traffic off my main network. While I don’t know how your WiFi plugs work, it is possible that they are talking to the cloud and the Echo is talking to the cloud as well with a persistent connection which would explain why things work.
Hey Scott,
thanks for the reply. i think you are correct - alexa seems to control the speakers from sending on/off to the TP link cloud, which then sends on/off to the device. Kind of stupid i wish it just pinged via lan.
either way, setting up this guest VLAN should address the security concerns i raised earlier right?
The Guest VLAN appears to meet all your needs. However, I’m not a security expert, so I can’t say for sure.
No problem. Lastly, for my own future reference, how were you able to figure out what the VLAN tag was for the airport? Would be useful for me down the road should I end up adding other access points. Thanks!
I found the VLAN ID online; not sure where. Different APs implement guest networks in different fashions and not all use VLANs.
@RP, the vlan tag 1003 seems to be what the Airport assigns to guest network. This works well for me.
Scott, Thanks for all this great info. I have set up an Edgerouter x with only one lan. I have an Airport Express with internal and guest network on eth1 and Netgear swithes on eth2 &3 for my internal network. Followed your Vlan 1003 and firewall instructions. I established the VLAN at the switch level, switch0.1003. I assigned the LAN post in the GuestIn firewall rule as 192.168.1.1. Wireless Guest network gets blocked from access to the router and files on computers on the internal network. However, if I disconnect the the guest network on the wireless devise then re-connect to the guest network, I can now access files on the internal network. I get the firewall protection on the initial connect to the guest network but lose the protection after disconnect/reconnect. Any thoughts would be greatly appreciated. Thanks. Ted
Hi Ted,
Unfortunately I’m not familiar with how the EdgeRouter X handles switch ports. However, establishing the VLAN at the switch level doesn’t seem right as your switch port would have to handle internal and guest network traffic. You might try adding the VLAN to eth1 where you have the Airport Express plugged in so you get eth1.1003 and then make sure the firewall rules are on eth1.1003.
@Ted, Is your ER-X connected to the WAN port on the Airport? I believe the VLAN tags are passed out there, segregated from the LAN ports. I have this setup working, with VLAN.1003 set up on both my L2 switch and the ERL (I have a LAN + VLAN on the same port from switch to ERL, because it only has 3 ports). I’m not familiar with your netgear switches, but I’d look there after the Airport physical connection.
Jon,
Thanks for reply. Yes, I have the wan port of the Airport connected to eth1 on the ER-X. eth1 is part of switch0. The firewall rules work, but if I disconnect and reconnect the guest wifi on the laptop, the firewall rules no longer prevent the laptop from accessing files on eth2 (also connected to switch0).
Ted
Hi Ted,
As Jon mentioned, you want to connect the AirPort’s LAN port to the ER-X otherwise the VLAN 1003 doesn’t get passed. I’m not sure why you’re seeing the behavior you’re seeing, but setting it up this way will be a big help. Also the AirPort needs to be in bridge mode and NOT hand out DHCP addresses. Give that a try and see what happens.
Scott/Jon,
Changed the physical connection from the ER-X eth1 to Airport Express LAN port (vs. WAN port) and had, and still have, Airport Express configured in bridge mode. Guest Network is blocked from internet until the vlan interface for 1003 on switch0, DHCP server and DNS listen interface added. Un-managed switch connected to eth2 with machine (PC#1) where I have set up Windows 10 file sharing with a shared drive defined. From another widows 10 machine (PC#2), via Airport Express/eth1 primary/non-guest network, I have mapped a network drive to the shared drive and am able to access files on the shared network drive defined on the PC#1. My objective is to not be able to access this shared drive from PC#2 attached via Airport Express/eth1guest network. From PC#2 I have been able to access the mapped network drive both before the VLAN was defined and after the VLAN was defined. Defining the Guest_In and Guest_Local firewall rules as defined in Scott’s blog don’t have any effect on blocking this access. As always, thanks for any thoughts you have. Like most seem to say, I too am new to this networking stuff and greatly appreciate your involvement.
Ted
I just finished checking my airport configuration and it’s not what I expected. Although I cannot ping to or from Guest VLAN, my network scanning software displays my ERL three times–with all three subnet IP addresses?? (e.g.: 10.0.0.1, 10.0.2.1, 10.0.3.1) I guess that doesn’t help you though. :(
Here’s what I see in my Airport config, starting with “Internet”– Connect: Static IPV4: 10.0.0.3 Mask: 255.255.255.0 Router: 10.0.0.2 (I somehow came to put this in here instead of the router IP to solve a past problem) DNS: 10.0.0.1 The rest is blank. Internet Options: Config IPV6: Automatically, Mode: Native
Wireless: Create a wireless network…
- Enable Guest Network… check
- both use WPA2 and obviously different SSIDs.
- Wireless option: nothing special–automatic
Network: Router Mode: OFF (bridge)
Physical: I have only 1 cable plugged into the WAN port. I believe that is the only place guest network traffic is routed, and with the VLAN tag.
This just occurred to me: can you confirm your switch gear is VLAN aware and handles the tags correctly? I remember that I bought my nice switch setup because you need a switch that’s smart enough to handle VLAN tags. I suspect your switch strips them off….
Hi there,
I cannot thank you enough for detailing all the steps in a way that I could follow along and succeed! I know that you’ve since moved on to other devices but wonder if you might have similar clear ideas of how to share a printer between the guest and the home network.
Could it be as simple as assigning different subnets to similar private IP ranges?
Many many thanks, Constantin
Hi Constantin,
Unfortunately I don’t have an easy answer for how to set this up as it is something I’ve never tried. Just setting up similar private IP ranges isn’t going to work as the guest network is specifically isolated from the rest of your LAN. You’ll have to setup firewall rules that allow traffic to your printer from the guest network. There are some posts on the Ubiquiti Forums that may help you.
Good luck!
Hi Scott,
Thanks again for this write up. I checked in over at UBNT and with some forum crawling came to a conclusion that prints…. The only caveat is mDNS and hence auto printer discovery does not work by default across these private networks, it apparently has to be enabled via the CLI.
Once I verify that the printer becomes plug and play even on the guest network, would you like me to post an update and how-to here?
Hi Constantin,
If you could post an update here, that would be great! While your exact steps would differ from mine on the USG, they will be similar.
Thanks!
In this set up do devecies on the guest network have access to each other?
I share a network with my neighbour. I’d like to set it up so that we are on two seperate vlans both with access to the internet, but not to each others vlans.
There is a hard wired wifi access point to the main router for each of our homes.
Seems I can follow these directions and basically put my neighbour on the “Guest Network”
Hi Alan,
Separate VLANs are the way to go. However, by default (without extra firewall rules), the main LAN can access the other VLANs. If you have control over the router and are just worried about your neighbor seeing your network and not vice-versa, then my instructions should work fine. Just like I added a rule to prevent the guest network from accessing the main network, you can add a rule that prevents the main network from accessing the guest network.
Good luck!
Thanks for the quick reply.
Makes sense. I would like to isolate completely, both my neighbor and I have various network media devices, chrome cast, apple tv etc. It can be annoying to output to a device in the wrong house.
I’ve solved this for now with a couple old consumer routers, but not without double Nat for atleast one of us.
As a software developer myself I prefer the proper solution.
On a slightly other note, Is there a reason you choose the edgerouter lite over the X.
The x is half the price and seems comparable.
Hi Alan,
I don’t know when the X came out, but a co-worker pointed me to the Lite and was quite pleased with the performance, so I went with his recommendation. I haven’t used the EdgeRouter Lite in about 9 months as I’ve switched to the UniFi Security Gateway; this is basically the same hardware as the EdgeRouter Lite, but integrated into the UniFi management.
Thanks you very much! A very useful process.
In Step 3, if you specify an external DNS like Google’s 8.8.8.8 or Cloudflare /APNIC’s 1.1.1.1 or whatever one is provided by your ISP, you do not need to set up the Firewall rule in Step 7 for local DNS on UDP port 53.
That saved me a step.
Thanks for the note! Local DNS provides some caching, so it will be faster than other servers if the entry is cached, however.